PG: Bratarina
| ターゲット // Bratarina | |
|---|---|
| Platform | OffSec Proving Grounds |
| OS | Linux |
| Difficulty | Easy |
| IP | 192.168.206.71 |
Recon#
Nmap#
| |
▶ Full nmap output
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3
25/tcp open smtp OpenSMTPD
|_ 2.0.0 This is OpenSMTPD 2.0.0
53/tcp closed domain
80/tcp open http nginx 1.14.0 (Ubuntu)
|_http-title: Page not found - FlaskBB
445/tcp open netbios-ssn Samba smbd 4.7.6-Ubuntu
Enumeration#
Port 80 - Web App (FlaskBB)#
A Flask-based forum. No useful content, weird behavior with empty Host: header. Rabbit hole – moving on.
Port 445 - SMB#
| |
backups READ ONLY Share for backups
└── passwd.bak
Downloaded passwd.bak – it’s just a copy of /etc/passwd. Another rabbit hole.
Port 25 - SMTP#
[ フラグ ]
This is the attack vector. OpenSMTPD 2.0.0 is ancient and has known RCE vulnerabilities.
| |
Foothold#
OpenSMTPD RCE (CVE-2020-7247)#
Found an exploit on ExploitDB. First, validate RCE with a ping:
| |
Confirmed via tcpdump. Now for a shell – the tricky part. The exploit doesn’t handle special characters well (<, >, |, & are all problematic):
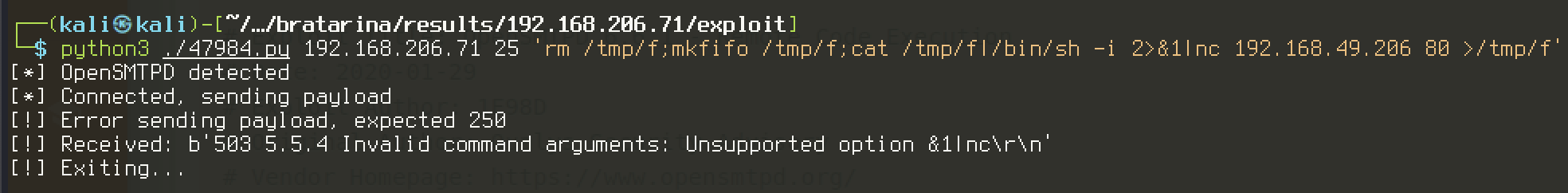
[ 警告 ]
Most reverse shell one-liners won’t work here because the exploit chokes on special characters. Python’s
subprocess module with escaped quotes is the way to go.The working payload – escape all commas in the Python reverse shell:
| |
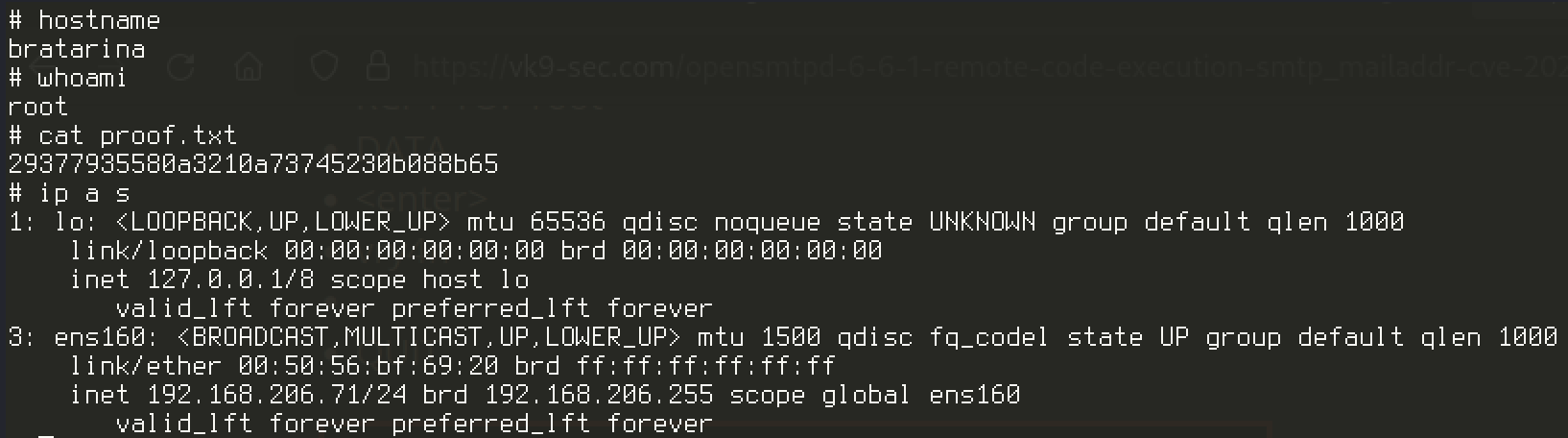
Privilege Escalation#
No privesc needed – the OpenSMTPD exploit lands us directly as root.
Proof#
proof
local.txt: [redacted]
proof.txt: [redacted]
Key Takeaways#
[ ノート ]
- Enumerate all service versions thoroughly – the web app and SMB were rabbit holes, SMTP was the way in
- When exploit payloads break due to character escaping, try Python’s
subprocessmodule with carefully escaped quotes - OpenSMTPD 2.0.0 is critically vulnerable – always check for known CVEs on outdated services