PG: Banzai
| ターゲット // Banzai | |
|---|---|
| Platform | OffSec Proving Grounds |
| OS | Linux |
| Difficulty | Medium |
| IP | 192.168.89.56 |
Recon#
Nmap#
▶ Full nmap output
20/tcp closed ftp-data
21/tcp open ftp vsftpd 3.0.3
22/tcp open ssh OpenSSH 7.4p1 Debian 10+deb9u7 (protocol 2.0)
25/tcp open smtp Postfix smtpd
5432/tcp open postgresql PostgreSQL DB 9.6.4 - 9.6.6 or 9.6.13 - 9.6.19
8080/tcp open http Apache httpd 2.4.25
8295/tcp open http Apache httpd 2.4.25 ((Debian))
Enumeration#
Port 21 - FTP#
No anonymous access. No public exploits for vsftpd 3.0.3 (aside from DoS).
Port 25 - SMTP#
User enumeration with Hydra and smtp-user-enum revealed standard system accounts plus admin, ftp, mysql, postgres.
Port 8080 & 8295 - Web Apps#
Two Apache instances. Port 8295 hosts a web application.
Foothold#
Weak FTP Credentials#
Tried common creds on FTP and got in with admin:admin.
The FTP root maps to the web application’s document root on port 8295. Uploaded a PHP command shell:
| |
Privilege Escalation#
MySQL UDF (User Defined Functions)#
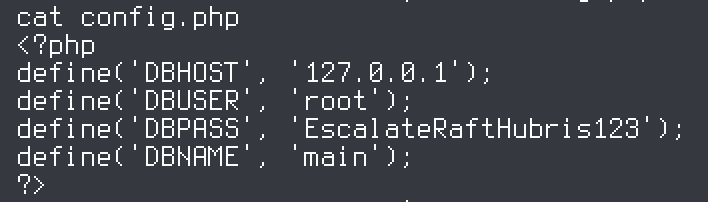
In the web root, one directory up from our landing, there’s a config.php with MySQL credentials: root:EscalateRaftHubris123.
Checking the MySQL config:
| |
MySQL is running as root. This means we can escalate via UDF.
UDF Exploitation Steps#
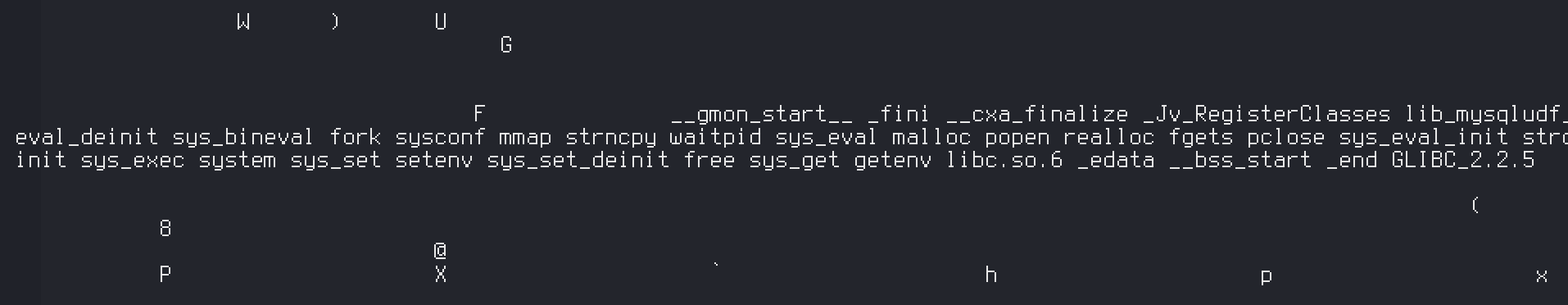
- Located the malicious library:
| |
Uploaded
lib_mysqludf_sys.so(x64, from Metasploit) to/var/www/on the target.Loaded it into MySQL:
| |
- Created a SUID bash:
| |
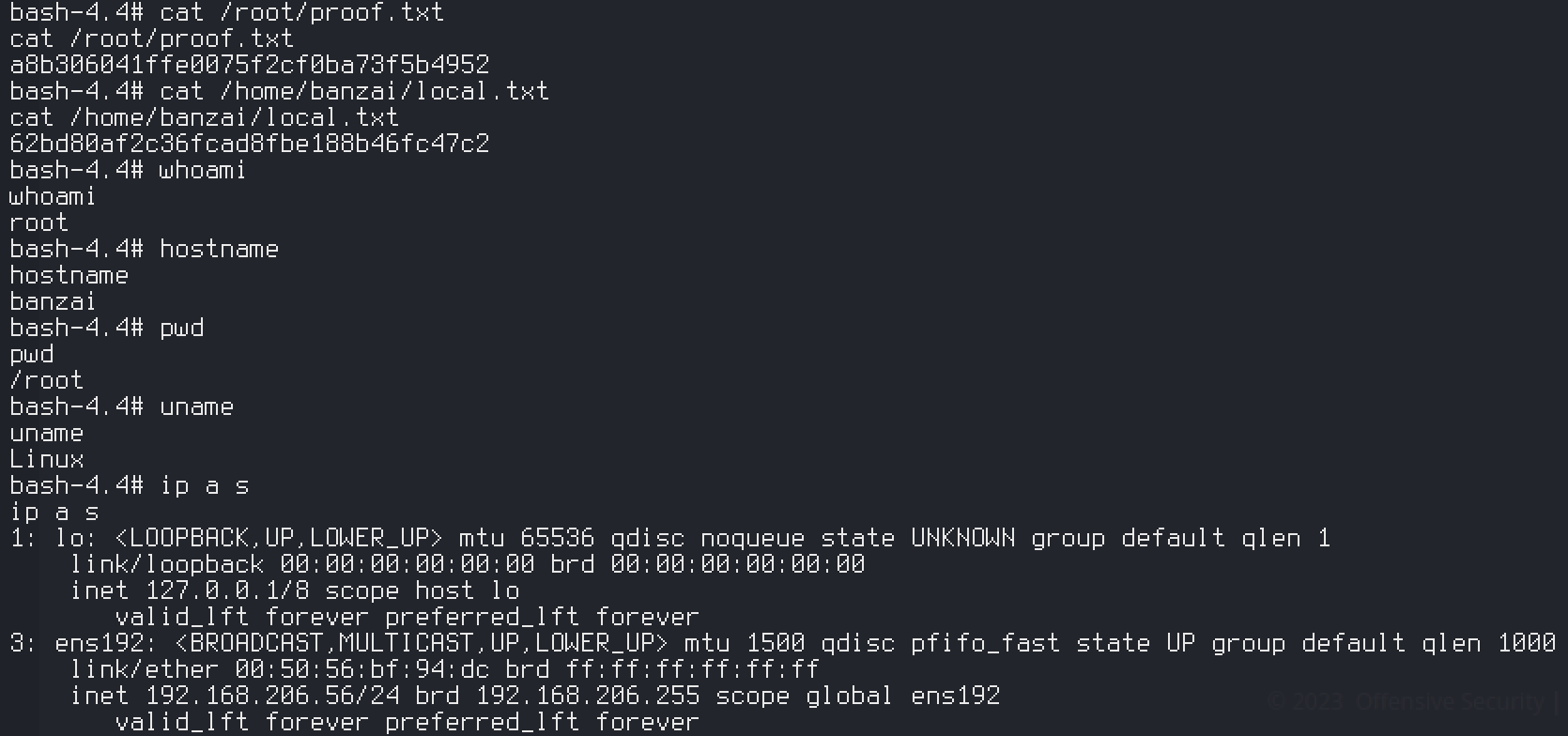
Root.
Proof#
proof
local.txt: [redacted]
proof.txt: [redacted]
Key Takeaways#
[ ノート ]
- Always try default/weak credentials on services like FTP (
admin:admin) - When FTP root maps to a web root, it’s a direct path to code execution
- Check what user MySQL runs as – if it’s root, UDF is a reliable privesc path
- Look for database credentials in web application config files (
config.php,.env, etc.)