HTB: Busqueda
| ターゲット // Busqueda | |
|---|---|
| Platform | HTB |
| OS | Linux |
| Difficulty | Easy |
| IP | 10.129.228.217 |
Recon#
Nmap#
| |
▶ Nmap output
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.1
80/tcp open http Apache httpd 2.4.52
Requests to the IP get redirected to searcher.htb – add it to /etc/hosts.
Enumeration#
Port 80 - Web App#
Nuclei picks up Python as the backend tech. The web app is a search aggregator. At the bottom of the page we spot the tech stack: Searchor 2.4.0.
Quick research reveals that Searchor before version 2.4.2 is vulnerable to command injection via the eval() function.
Foothold#
Searchor 2.4.0 - Command Injection#
Testing for CI with a crafted POST request:
| |
uid=1000(svc) gid=1000(svc) groups=1000(svc)
We have RCE. Time for a reverse shell:
| |
Paste into the search field, catch with netcat – we’re in as svc.
Privilege Escalation#
Git Credentials Discovery#
The web app directory contains a .git folder. Inside .git/config:
| |
Credentials: cody:jh1usoih2bkjaspwe92
Add gitea.searcher.htb to /etc/hosts to access the Gitea instance. The password also works for SSH as svc (password reuse).
Sudo Privileges#
| |
The script has three options: docker-ps, docker-inspect, and full-checkup.
Docker Inspect - More Credentials#
Using docker-inspect to dump the Gitea container config:
| |
From the JSON output:
| |
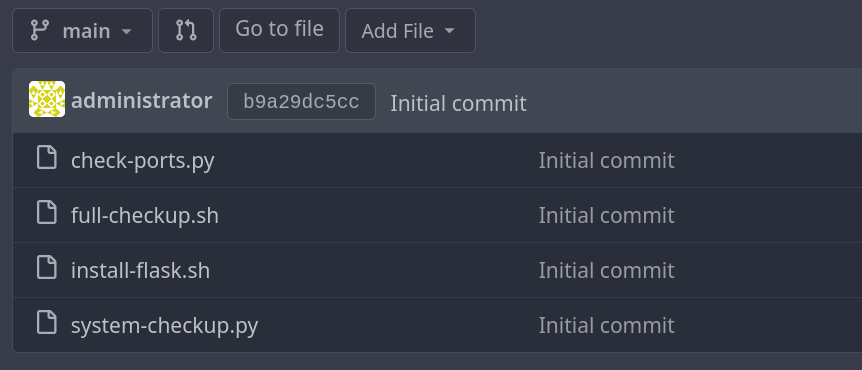
This password works for the Administrator account on Gitea. Inside we find the scripts repository with the actual source code:
Relative Path Exploitation#
Reviewing system-checkup.py source from Gitea:
| |
It calls ./full-checkup.sh with a relative path. If we run the script from a directory where we control a full-checkup.sh file, we can execute arbitrary code as root:
| |
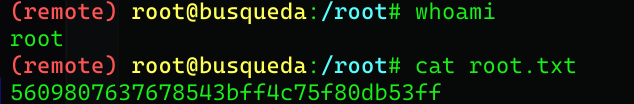
Root shell received.
Proof#
Credentials Collected#
| User | Password | Service |
|---|---|---|
| cody | jh1usoih2bkjaspwe92 | Gitea |
| svc | jh1usoih2bkjaspwe92 | SSH |
| gitea (db) | yuiu1hoiu4i5ho1uh | MySQL |
| Administrator | yuiu1hoiu4i5ho1uh | Gitea admin |
Key Takeaways#
- Always check
.gitdirectories for hardcoded credentials in config files docker inspectcan leak environment variables including database passwords- Relative path vulnerabilities in sudo scripts are an easy win – always check the source
- Password reuse across services is extremely common in real environments too